CLI Systems Virtual Subnets
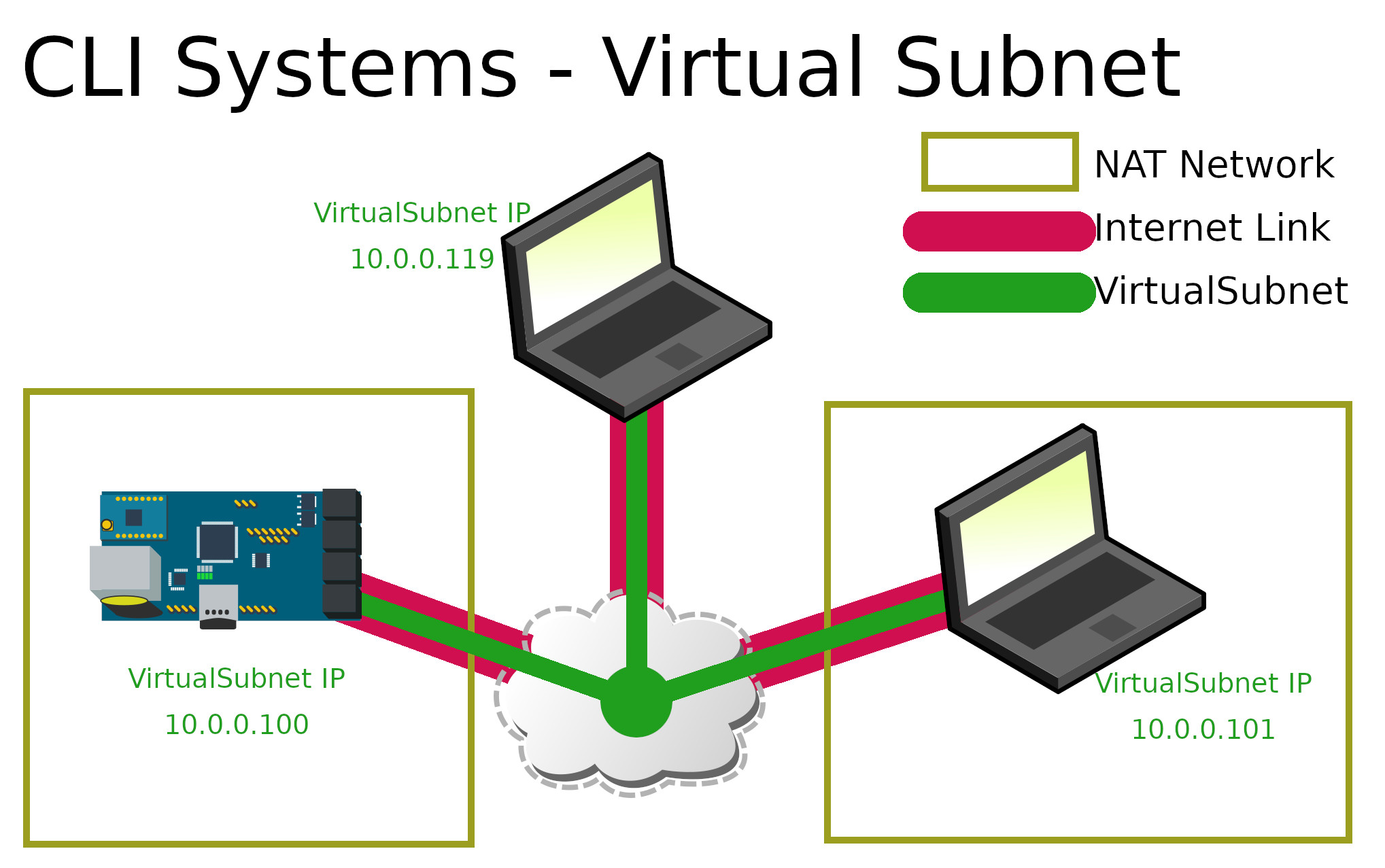
2 users and 1 device. Both users can
access the device
A 'virtual subnet' is like a VPN, but all devices on the subnet can access the other devices on the subnet. This allows devices that are located on different networks (or diffrerent sides of the world) to securely pass traffic as if they were on the same network.
CLI Systems's virtual subnets are built on the Wireguard VPN network protocol, which uses modern public key encryption to secure all traffic through the network links. Information and documentation on the Wireguard protocol can be found at https://wireguard.com.
VPN vs Virtual Subnet
Wireguard is used to create a virtual, secure, network link between a computer and a server. Typical uses for this type of virtual connection are commercial VPN solutions where the internet traffic from the computer is routed through the server to protect the IP source of the traffic. The CLI Systems virtual subnet creates the same type of virtual network link, however it is configured to route traffic of the local subnet. Typically VPN providers don't allow this type of routing since their networks are used by many people, or the VPN is tied in with an 'office LAN' which can cause security issues. This is why our solution is better described as a virtual subnet than a VPN.
Virtual Subnet PC Access
Individual PCs can be configured to connect directly to the virtual subnet using a local client on the PC. Wireguard clients exist for all major operating systems including Windows, Linux, OSX, iPhone, and Android. Each client has a unique public-private key set, granting them access to the network. Network access is easy to control by removing the client key in the server.
Virtual Subnet Nodes
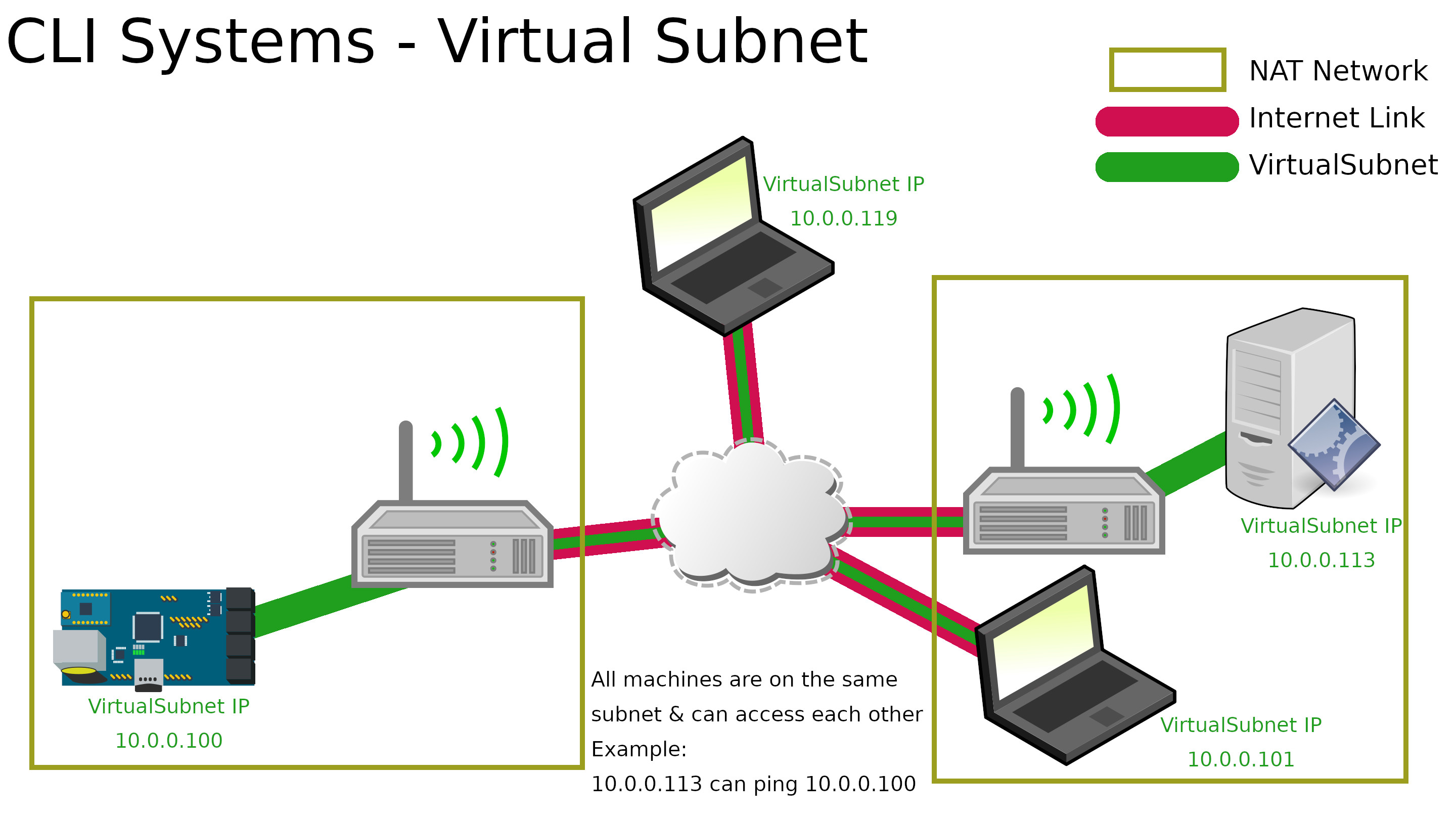
2 users, 2 Nodes, and 1 device attached
to each Node.
Not all devices can install a Wireguard client; for example engineering systems or off the shelf devices (sensors, data logger, etc). CLI Systems has developed a solution to allow basic network devices like that to access the virtual subnet without changing the firmware on the device. Virtual subnet 'Nodes' are routers that allow basic network devices to be on the virtual subnet by just connecting them via Ethernet or WiFi.
Nodes are clients of a virtual subnet network, and also provide DHCP and routing to a section of the network subnet. The Node is plugged in to the local network where it receives a local network IP address, such as 192.168.1.16. The Node is a client on the local network, but it is also configured to be on a virtual subnet Wireguard network.
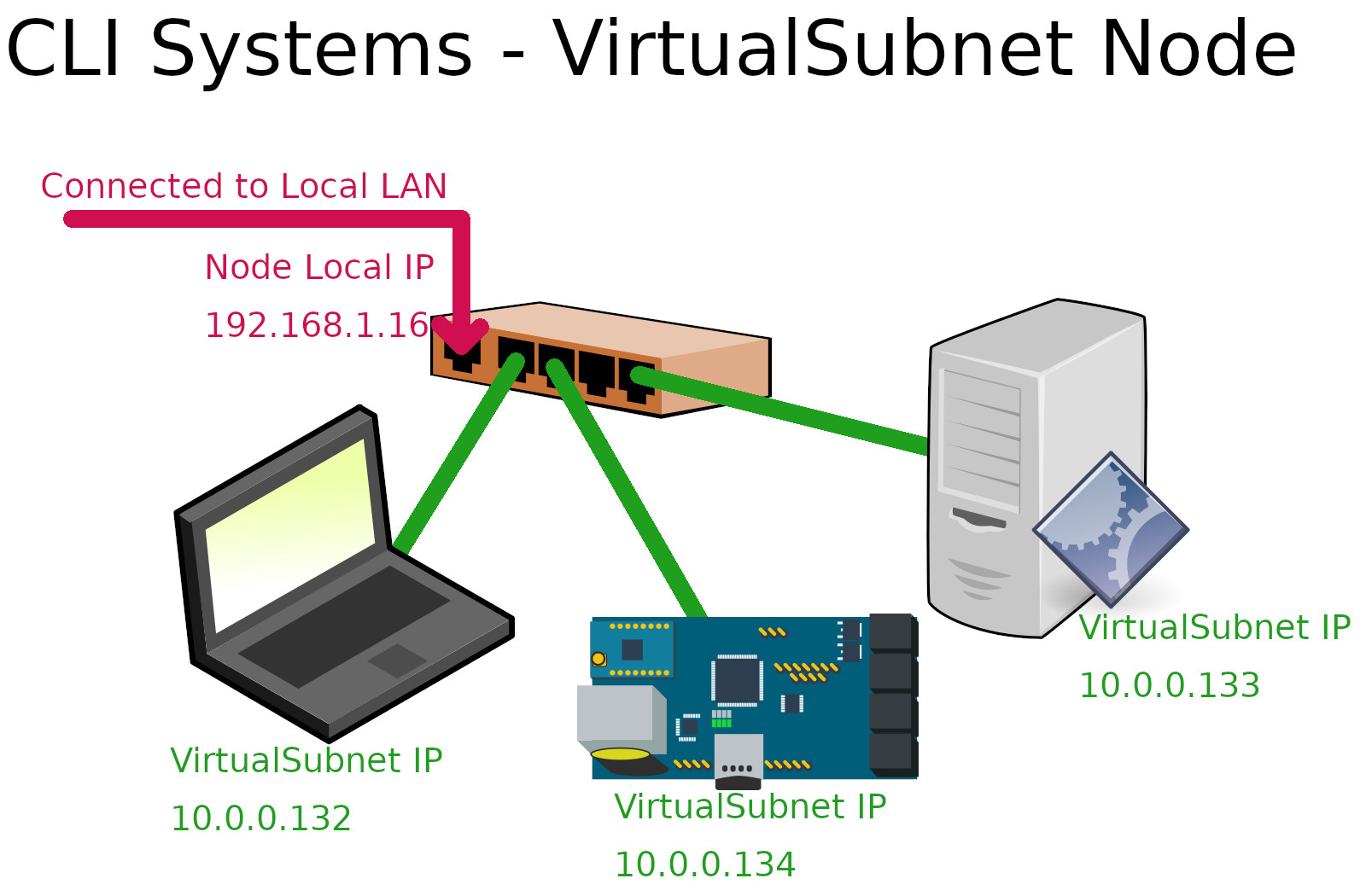
network providing virtual subnet IPs for
3 client devices.
The Node provides DHCP IP addresses on the output LAN ports for a section of the Wireguard subnet; for example it provides DHCP addresses 10.0.0.130 through 10.0.0.160. Devices that need to be on the virtual subnet are just plugged in to the LAN port of the Node where they receive an IP between 10.0.0.130 and 10.0.0.160. Once a device is connected to the virtual subnet it can ping the other devices, and the other device can access its resources.
Interested in a private virtual subnet for your business?
Want to speed up your engineering?
Yes, tell me more about this solution